Microsoft Defender vs Microsoft Sentinel
August 06, 2023 | Author: Michael Stromann
See also:
Top 10 SIEM software
Top 10 SIEM software
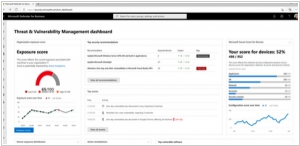
Microsoft Defender and Microsoft Sentinel are two security solutions offered by Microsoft, each designed to address different aspects of cybersecurity. Microsoft Defender, formerly known as Windows Defender, is an endpoint security platform focused on protecting individual devices and endpoints from various threats, including malware, viruses, and ransomware. It provides real-time protection, advanced threat detection, and automated response capabilities to safeguard Windows-based systems. On the other hand, Microsoft Sentinel is a cloud-native security information and event management (SIEM) solution, part of the Microsoft Azure ecosystem. Sentinel offers a centralized view of an organization's security landscape, utilizing advanced analytics and artificial intelligence to detect and respond to security incidents across the entire network. While Microsoft Defender concentrates on protecting endpoints, Microsoft Sentinel takes a broader approach, providing a comprehensive view of an organization's security posture and facilitating efficient threat detection and response across the entire infrastructure.
See also: Top 10 SIEM software
See also: Top 10 SIEM software
Microsoft Defender vs Microsoft Sentinel in our news:
2021. Microsoft launches Defender for Business
Microsoft has unveiled Microsoft Defender for Business, an innovative and affordable endpoint security solution designed specifically to cater to businesses employing up to 300 individuals. This new offering from Microsoft enhances security measures beyond traditional antivirus systems by providing next-generation protection, endpoint detection and response capabilities, threat and vulnerability management, and more. With simplified configuration and management, along with intelligent and automated investigation and remediation, Defender for Business ensures robust security. It safeguards against a range of cybersecurity threats, including malware and ransomware, across Windows, macOS, iOS, and Android devices. Available as a standalone solution, it can be obtained for a cost of $3 per user per month.
2019. Microsoft Defender comes to Mac
Microsoft Defender Advanced Threat Protection (ATP) will be available for Mac as well. Previously, it served as a Windows solution designed to safeguard the machines of Microsoft 365 subscribers and the assets managed by IT administrators. Formerly known as Windows Defender ATP, Microsoft has decided to drop the "Windows Defender" name since it is now accessible on Mac. Many enterprises utilize a combination of Windows and Mac machines and already equip their employees with Office. By having a security solution that covers both systems, IT departments can significantly simplify their operations, as managing security vulnerabilities on a single system is challenging enough as it is.
2016. Microsoft released Windows Defender Advanced Threat Protection
WDATP is a cloud service offered by Windows Defender, the built-in antivirus in Windows. Currently, Windows Defender primarily focuses on scanning websites and downloads to prevent hacking attempts. However, in the era of social engineering and spear-phishing, antivirus software needs to adopt a more proactive approach. Windows Defender Advanced Threat Protection (WDATP) aims to address this by shifting its attention from monitoring individual files to observing the overall behavior of a machine. Instead of simply searching for specific viruses, WDATP keeps a close watch on symptoms that indicate potential threats. For instance, if a machine starts establishing connections with unusual ports or executing uncommon PowerShell commands—behavior that deviates from the norm for most users—WDAPT alerts administrators. It provides them with an overview of both current and historical machine behavior for further analysis. Moreover, Microsoft is capitalizing on the extensive Windows user base to jumpstart its antivirus program. By analyzing millions of suspicious files from machines worldwide in the cloud, a vast centralized database is being constructed, encompassing not only malicious files but also malicious behavior.